2026 HIPAA Security Rule: What Home Healthcare Agencies Need to Know

97 articles

UnitedHealth Group delivered 19 million in-home visits in 2025. For home healthcare agencies, this signals a permanent shift in care delivery — and a rising standard for cybersecurity, HIPAA readiness, and digital resilience.
Read More
Home care agencies are carrying more digital responsibility than ever before. Patient records, schedules, billing information, caregiver communication, payroll, referral data, and family updates now move across multiple systems —…
Read More
Introduction: Attacks No Longer Happen in One Place Cyberattacks used to be simple. An attacker sent a malicious file, it landed on an endpoint, and antivirus software either stopped it,…
Read MoreIntroduction: Not All Data Loss Comes from Hackers When organizations think about data loss, they often picture external attackers breaking into systems and stealing information. In reality, many of today’s…
Read More
Introduction: The Inbox Is Still the Front Door Despite years of investment in cybersecurity tools, email remains the number one entry point for cyberattacks . Phishing, business email compromise (BEC),…
Read More
Silent data loss often goes undetected until retention policies expire and recovery is no longer possible. This real‑world recovery scenario shows why immutable backups are essential for long‑term protection and how ShieldForce ensures data integrity beyond native platform limits.
Read More
In July 2025, global technology distributor Ingram Micro disclosed a ransomware attack that resulted in a data breach affecting more than 42,000 individuals . The incident involved the theft of…
Read More
Why Silent Data Loss Demands Strong, Enforced Immutability
Read More
In May 2025, Covenant Health, a major healthcare provider operating across New England and parts of Pennsylvania, suffered a ransomware attack that ultimately impacted nearly 478,000 patients . What initially…
Read More
Cyberattacks directly affect revenue, trust, and operations. Learn why prevention is critical and how ShieldForce stops attacks before financial damage occurs.
Read More
Fake job and scholarship emails are on the rise. Learn how to recognize them and how ShieldForce prevents these scams.
Read More
Remote work expands the attack surface. Learn how ShieldForce protects users wherever they work, beyond the traditional office.
Read More
Security alerts alone don’t stop attacks. Learn how ShieldForce reduces real cyber risk by preventing threats before they cause damage.
Read More
Healthcare organisations are increasingly targeted by cyber criminals not only because of the value of patient data, but because healthcare systems often prioritize availability over security. The recent cyber-attack on…
Read More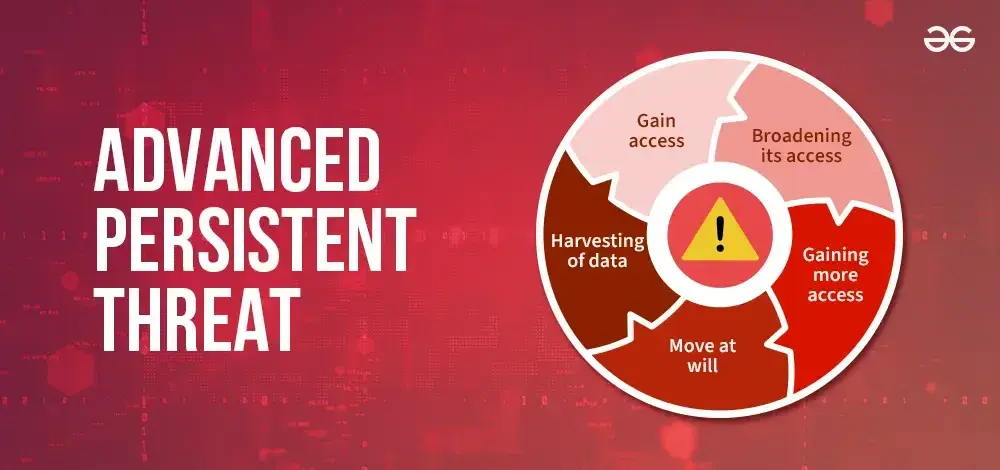
Advanced Persistent Threats (APTs) are silent, long term cyber attacks designed to steal data and disrupt operations. Learn how ShieldForce detects and stops APTs before damage occurs.
Read More
Students and young adults are prime targets for email scams. Learn how these attacks work and how ShieldForce helps protect vulnerable users.
Read More
2025 saw several Microsoft 365 service incidents affecting Exchange Online and Teams. In November 2025, customers across APAC and North America couldn’t connect to mailboxes via the classic Outlook desktop client. Earlier disruptions affected Teams' creation/federation and compliance with portal acc...
Read More
In July 2025, Microsoft confirmed that the actor Storm-2603 exploited on-premises SharePoint vulnerabilities to deploy Warlock ransomware. Although SharePoint Online in Microsoft 365 was not affected, attackers compromised hundreds of on-prem servers worldwide, including government agencies, illustr...
Read More
Since September 2025, multiple threat clusters, both financially motivated and state-aligned, have scaled a new wave of phishing that doesn’t steal passwords and doesn’t break MFA in the traditional sense. Instead, adversaries weaponize the legitimate OAuth 2.0 device code authorization flow by conv...
Read More
Multiple threat actors are compromising Microsoft 365 accounts in phishing attacks that leverage the OAuth device code authorization mechanism.
Read More
Bleeping Computer recently reported that a hacker claims to have leaked a Wired database containing 23 million records , including sensitive user information. While this breach didn’t originate from Microsoft 365, it underscores a universal truth: data breaches are inevitable when organizations rely...
Read More
Personal data has become one of the most valuable assets in the digital world. Information such as email addresses, passwords, bank details, and identity records can be exploited for fraud, identity theft, and financial crimes. Because of this, cybercriminals are constantly developing new ways to st...
Read More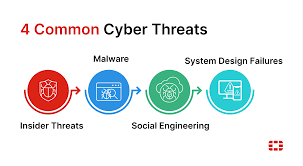
With more families relying on the internet for daily activities and remote work becoming the norm, cybercriminals are increasingly shifting their focus from large organizations to individuals and home networks. Families and remote workers often lack the advanced security protections used in corporat...
Read More
Many small businesses believe effective cybersecurity requires a large budget. While enterprise level security tools can be expensive, strong cybersecurity does not have to be out of reach. The key is knowing what to prioritize when resources are limited.
Read More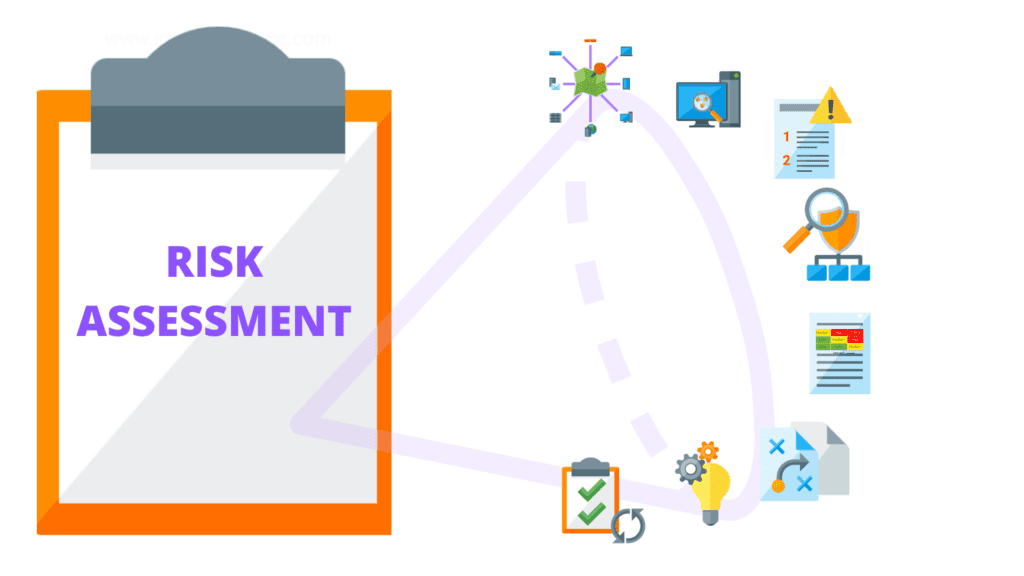
In today’s digital landscape, cyber threats evolve faster than most businesses can keep up. New vulnerabilities appear daily, attackers automate their tactics, and even a minor security gap can open the door to major disruptions. This is why regular security assessments are no longer optional, they ...
Read More
Email remains one of the most common ways cybercriminals reach their victims. As technology evolves, so do email scams, becoming more convincing, targeted, and harder to detect. In 2025, home users are facing increasingly sophisticated scams designed to steal personal information, money, and access ...
Read More
Children today grow up surrounded by technology. From online learning and gaming to social media and messaging apps, the internet plays a major role in their daily lives. While the digital world offers many benefits, it also exposes children to cyber risks that parents may not always be aware of.
Read More
Compliance isn’t just a checkbox; it’s the backbone of patient trust and operational integrity. HIPAA and FTC safeguards exist to protect PHI, ensure secure workflows, and prevent costly breaches. Yet many home healthcare agencies and small clinics struggle to translate these requirements into daily...
Read More
When a cyber incident strikes, ransomware, phishing compromise, or unauthorized access, the first hour determines everything: downtime, data loss, and regulatory exposure. Yet most healthcare agencies lack a structured response plan. This article outlines a six-step playbook for the critical first h...
Read More
Home health teams deliver care on the move between visits, over patient/home Wi-Fi, and on devices that often carry PHI locally. Attackers target these uncontrolled environments with phishing, exploit kits, and credential theft. Effective defense begins at the endpoint with
Read More
Healthcare runs on communication orders, discharge summaries, lab results, and payer updates. That makes email the most convenient workflow tool and the most abused attack vector. In home healthcare and small clinical settings, inboxes are constantly hit by phishing , business email compromise (BEC)...
Read More
Your EMR is the clinical heartbeat capturing orders, charting, history, billing, and coordination with partners. That centrality and the sensitive data it holds make EMR platforms a prime target. An exploit, misconfiguration, or credential compromise can ripple across visits, documentation, and reim...
Read More
Data privacy isn’t a feature; it’s a design principle. In healthcare, where PHI flows across clinicians, patients, and partners, privacy must be embedded into every workflow. Yet many agencies treat privacy as an afterthought, relying on ad-hoc controls that fail under pressure. This article explain...
Read More
Home healthcare thrives on mobility; clinicians move between homes, update charts on laptops or tablets, and access EMR systems remotely. But every time care happens on patient Wi-Fi or public hotspots , the risk of compromise skyrockets. Attackers exploit weak encryption, shared networks, and outda...
Read More
Many small businesses believe they are too small to be targeted by cybercriminals. Unfortunately, this assumption is one of the biggest cybersecurity mistakes a business can make. Small businesses often lack dedicated security teams and advanced protection, making them attractive targets for attacke...
Read More
In healthcare, downtime isn’t just inconvenient; it’s dangerous. Yet many agencies rely on manual backups or untested recovery plans that fail under pressure. Ransomware, accidental deletions, or hardware failures can erase vital patient records instantly. This article explains why traditional backu...
Read More
Home healthcare agencies deliver care through mobile teams, portable devices, and multi- party data exchanges . That clinical reality care delivered in patients’ homes, often on untrusted Wi-Fi, expands the attack surface for threats like phishing/BEC, ransomware, credential theft, exploit chains, a...
Read More
If you’re looking for how to get in touch with ShieldForce customer support in Australia, the good news is that the process is simple and accessible. ShieldForce operates as a fully remote service provider, which means you do not need to visit any physical office or wait for local branch hours befor...
Read More
ShieldForce is a cybersecurity solution provide and not a physical security provider. ShieldForce services include endpoint protection, ransomware protection, data backup and disaster recovery, email security, vulnerability assessments, and other managed digital security solutions.
Read More
Cybersecurity issues can’t wait, and neither should you. At ShieldForce, we pride ourselves on providing 24/7 customer support to ensure your business stays secure and operational at all times.
Read More
Cyber threats are evolving faster than ever. Ransomware, zero-day exploits, and phishing attacks can cripple businesses in minutes. ShieldForce takes a layered approach to threat detection , combining multiple security engines into one platform to identify and neutralize threats before they cause ha...
Read More
Cybersecurity isn’t one-size-fits-all. Different industries face unique challenges, from compliance requirements to operational risks. ShieldForce understands this and offers customized security solutions for industries that depend on IT infrastructure . Here’s how we help.
Read More
Small businesses are increasingly targeted by cybercriminals because they often lack dedicated IT teams and enterprise-grade security. ShieldForce changes that by delivering managed security services tailored for SMBs that are affordable, scalable, and easy to deploy.
Read More
ShieldForce December Black Friday Cyber Savings - Up to 50% Off!
Read More
Choosing the right cybersecurity partner can make or break your business’s resilience. While many providers offer partial solutions, ShieldForce delivers comprehensive protection on a single platform with transparent pricing and human-centered security.
Read More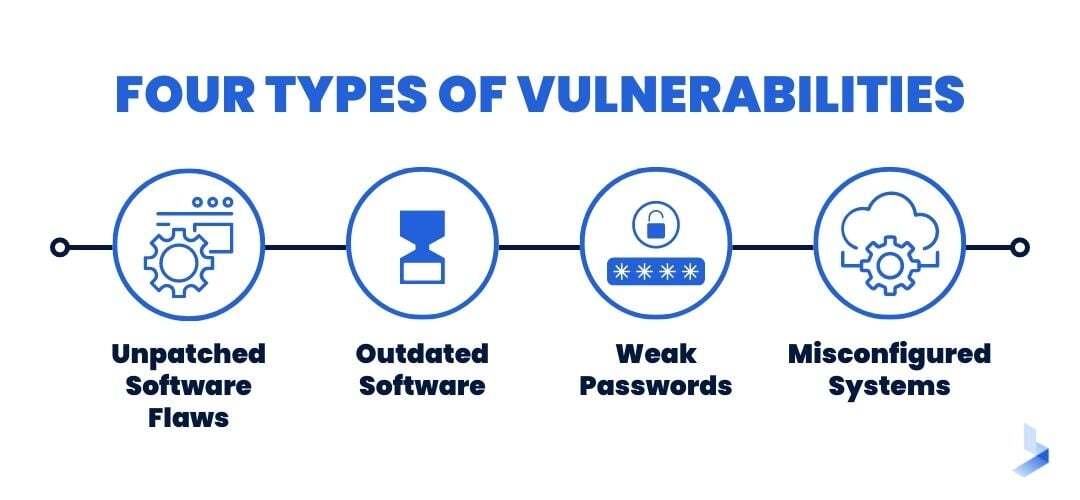
Protect your business from cyber risks and secure your sensitive information.
Read More
In today’s digital world, businesses face relentless cyber threats that can lead to financial losses and reputational damage. ShieldForce is designed to stop breaches before they start and ensure rapid recovery if they occur. But what exactly does ShieldForce offer? Let’s dive in.
Read More
ShieldForce Pricing: Affordable Cybersecurity for Every Business Size
Read More
In today’s digital landscape, cyber threats evolve faster than most businesses can keep up. New vulnerabilities appear daily, attackers automate their tactics, and even a minor security gap can open the door to major disruptions. This is why regular security assessments are no longer optional, they ...
Read More
Email remains the primary communication tool for home healthcare agencies, used daily for scheduling, sharing patient updates, coordinating care teams, and communicating with families and physicians. But while email keeps operations running, it is also the number one attack vector cybercriminals use...
Read More
Home healthcare is built on trust, trust that caregivers will show up, provide quality care, and protect patients' most personal information. But in today’s digital world, protecting patient data requires more than compassion. It requires cybersecurity awareness.
Read More
What your agency needs to know and how to stay protected. Home healthcare agencies are becoming one of the top targets for cybercriminals in 2025. Why? Because they collect sensitive patient information, rely heavily on mobile caregivers, and often don’t have the same security resources that large h...
Read More
In home healthcare, communication is everything. Caregivers share updates with hospitals, send lab information, coordinate with physicians, and report patient progress all while working outside the controlled environment of a clinic. This constant flow of information is essential for delivering qual...
Read More
Understanding why the healthcare sector is the most attacked industry—and why home-based care faces even greater risks. Home healthcare is transforming how patients receive care—bringing comfort, flexibility, and personalized medical attention right to their doorstep. But as home healthcare becomes ...
Read More
As home healthcare continues to shift toward mobile and remote service delivery, cybersecurity risks are rising just as quickly. Caregivers now log in from different patient homes, use various WiFi networks, and rely heavily on mobile devices to access schedules and patient records. This level of mo...
Read More
Strengthen healthcare cybersecurity, protect patient data, and ensure HIPAA compliance with ShieldForce’s expert solutions and practical security tips.
Read More
Home healthcare agencies rely on mobile devices, cloud systems, and remote workers to deliver care. Learn how EDR solutions help strengthen endpoint security, reduce ransomware risk, and support HIPAA-aligned cyber resilience.
Read More
ShieldForce EDR protects financial institutions with real-time threat detection, automated response, and compliance-ready endpoint security.
Read More
Discover how XDR transforms cybersecurity by integrating data across systems to detect and respond to threats faster and more effectively
Read More.jpg)
Learn why every business needs a disaster recovery plan to protect data, ensure resilience, and maintain customer trust in today’s threat landscape.
Read More.jpg)
Discover how policy automation reduces human error, strengthens cybersecurity, and ensures consistent compliance across your business operations.
Read More.jpg)
Explore key features of effective data privacy solutions that protect sensitive business information and ensure regulatory compliance.
Read More.jpg)
Discover best practices for secure team collaboration that protect sensitive data while boosting productivity and trust across your organization.
Read More
The Unseen Vulnerability: Protecting Patient Care in a Digital World
Read More
Shift to a proactive cybersecurity strategy. Learn the pillars: Zero Trust, XDR, and Threat Intelligence to ensure cyber resilience and minimize costs.
Read More
Discover affordable cybersecurity strategies for small healthcare and financial businesses in 2025. Learn budget-friendly tips to protect data, ensure HIPAA/PCI DSS compliance, and build customer trust.
Read More
Real estate is a prime target for cybercrime. Discover hidden risks in the property deals and how to protect your firm from costly breaches.
Read More
Learn top expert tips to avoid a $2M cybersecurity vulnerability and protect your business effectively.
Read More
How SMBs can improve their Security Postures by implementing Zero Trust Technologies.
Read More
How SMBs can Increase their Security Posture By Implementing Automation
Read More
Keeping up to date with Trends in Phishing Attack and Exploring Effective Strategies for Prevention, Detection and Response
Read More
Top Ten Techniques to Protect your Small Business from Cyber Attacks and Remain Security Conscious
Read More
How to Protect your WhatsApp account and Retrieve Hacked Account
Read More
Top 10 Techniques to Protect your FaceBook account from Hackers
Read More
Top Security Challenges and Risk associated with the increase in Connected IoT Devices
Read More
ShieldForce Cybersecurity Service Now Available in the Microsoft Azure Marketplace
Read More
Application of Machine Learning in Cybersecurity for Small Business
Read More
Top 15 Techniques to Protect your Workstation from Ransomware and Malware.
Read More
Top Ten ways Small Businesses can Protect their Mobile Devices from Cyber Attackers
Read More
Top 10 Anti-virus and Anti-Malware Software in 2024
Read More
Application of Artificial Intelligence in Cybersecurity for SMBs
Read More
Complex Systems and Database Security: An Introduction
Read More
Common Cybersecurity Concepts that might save your Business from a Cyber Attack
Read More
ShieldForce Press Release - ShieldForce rolls out Cybersecurity subscription plans into US Market
Read More
Cloud Security guidelines for eCommerce based businesses
Read More
The Role of Cybersecurity in the Modern World
Read More
Continuous User Authentication: Effective against Social Engineering Attacks
Read More
The Las Vegas Cyber Attacks: How to Apply Lessons Learned and Protect your Company
Read More
Top 10 Shocking Cybersecurity Strategies used by Nigerian Scammers to target US Based Businesses
Read More
FTC Safeguards rules that can cost your car dealership over $250,000 in fines and penalties in the United States
Read More
Top 10 Cybersecurity Pain points and Challenges faced by Car Dealerships in the United States
Read More
Top 15 Secret Information Technology Policies Revealed to Protect your Organizations Information Assets from Financial losses and Reputational damage.
Read More
Top Secret Cybersecurity Strategies revealed to protect your human resources department from financial losses and reputational damage.
Read More
Top 10 Secret Cybersecurity Strategies Revealed to protect your workstations from financial losses and reputational damage through social engineering.
Read More
Top 10 Secret Cybersecurity Strategies revealed for protecting your employees from Financial Losses and Reputational damage.
Read More