
How ShieldForce Extends Protection Beyond the Office
Remote work expands the attack surface. Learn how ShieldForce protects users wherever they work, beyond the traditional office.
Read articleAuthor Archive
15 articles written by Azeezat Lawal.
A focused archive without featured content or extra filters.

Remote work expands the attack surface. Learn how ShieldForce protects users wherever they work, beyond the traditional office.
Read article
Cyberattacks directly affect revenue, trust, and operations. Learn why prevention is critical and how ShieldForce stops attacks before financial damage occurs.
Read article
Fake job and scholarship emails are on the rise. Learn how to recognize them and how ShieldForce prevents these scams.
Read article
Security alerts alone don’t stop attacks. Learn how ShieldForce reduces real cyber risk by preventing threats before they cause damage.
Read article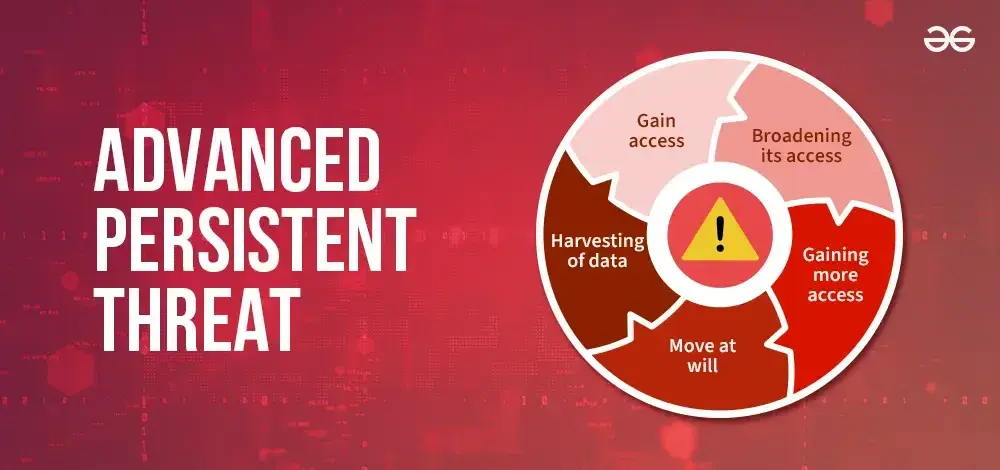
Advanced Persistent Threats (APTs) are silent, long term cyber attacks designed to steal data and disrupt operations. Learn how ShieldForce detects and stops APTs before damage occurs.
Read article
Personal data has become one of the most valuable assets in the digital world. Information such as email addresses, passwords, bank details, and identity records can be exploited for fraud, identity theft, and financial crimes. Because of this, cybercriminals are constantly developing new ways to st...
Read article
Email remains one of the most common ways cybercriminals reach their victims. As technology evolves, so do email scams, becoming more convincing, targeted, and harder to detect. In 2025, home users are facing increasingly sophisticated scams designed to steal personal information, money, and access ...
Read article
Many small businesses believe effective cybersecurity requires a large budget. While enterprise level security tools can be expensive, strong cybersecurity does not have to be out of reach. The key is knowing what to prioritize when resources are limited.
Read article
Many small businesses believe they are too small to be targeted by cybercriminals. Unfortunately, this assumption is one of the biggest cybersecurity mistakes a business can make. Small businesses often lack dedicated security teams and advanced protection, making them attractive targets for attacke...
Read article
If you’re looking for how to get in touch with ShieldForce customer support in Australia, the good news is that the process is simple and accessible. ShieldForce operates as a fully remote service provider, which means you do not need to visit any physical office or wait for local branch hours befor...
Read article
Protect your business from cyber risks and secure your sensitive information.
Read article
What your agency needs to know and how to stay protected. Home healthcare agencies are becoming one of the top targets for cybercriminals in 2025. Why? Because they collect sensitive patient information, rely heavily on mobile caregivers, and often don’t have the same security resources that large h...
Read article
Understanding why the healthcare sector is the most attacked industry—and why home-based care faces even greater risks. Home healthcare is transforming how patients receive care—bringing comfort, flexibility, and personalized medical attention right to their doorstep. But as home healthcare becomes ...
Read article.jpg)
Discover how policy automation reduces human error, strengthens cybersecurity, and ensures consistent compliance across your business operations.
Read article.jpg)
Explore key features of effective data privacy solutions that protect sensitive business information and ensure regulatory compliance.
Read article